New Member
September 12, 2014
Question
Intervlan Routing
- September 12, 2014
- 2 replies
- 45844 views
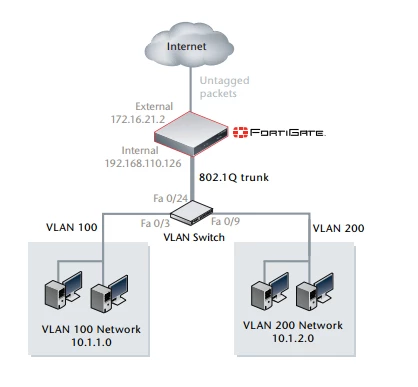
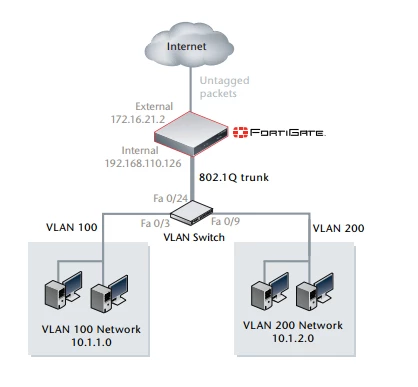
I have problem VLAN routing on fortigate 60D. I have create 2 subinterface (vlan100 and 200) in internal interface and cisco catalyst 2960s I have create 2 vlan (vlan100 and 200) with a trunk interface. and configure policy and firewall object for internet access, for vlan 100 can access internet and network is working normally, but vlan 200 cannot communicate with fortigate. I have verify that trunk interface is correctly configure on Cisco Switch. for topology as the image attachment here. Could anyone can recommend me what is missing, while one vlan is working normal and other vlan cannot communicate with fortigate. Thank for support