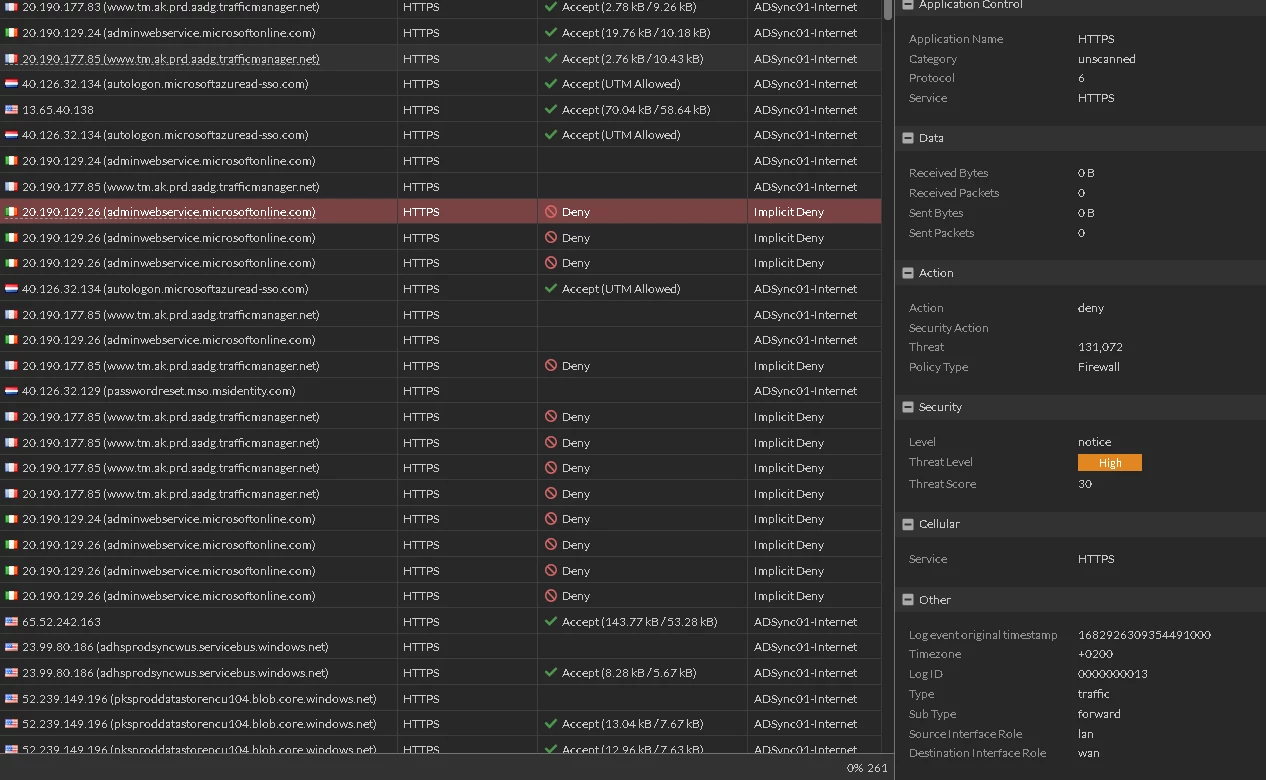
Blocked HTTPS Traffic
Hii
Could someone help me please to identify the problem
I don't know why this traffic is blocked and it affects our ADSync Server online syncronization
Hii
Could someone help me please to identify the problem
I don't know why this traffic is blocked and it affects our ADSync Server online syncronization
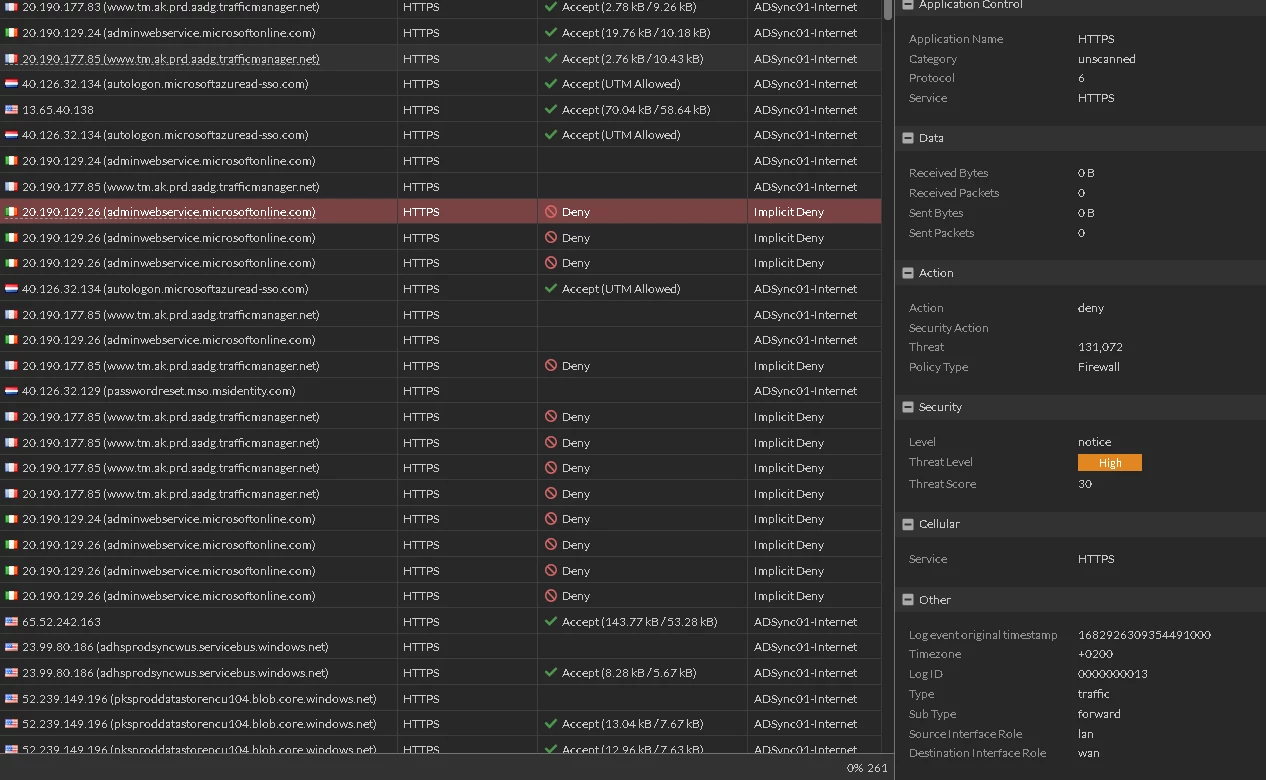
First remove the webfilter from the policy to see if it starts working in the first place. Based on the policy view there is no web filter applied at this time. Just to make sure.
If it fails working, there is no point troubleshooting anything on the webfilter since it has no direct affect. The traffic is blocked BEFORE the webfilter will be applied.
When the traffic is working fine, then apply webfilter etc. to the traffic. You will also need minimum certificate inspection, better a deep inspection as FortiGate can only block what it can read. Encrypted traffic cannot be read.
Next is that your initial screenshot show a different source interface (port1 vs port2). See if that is the pattern on the failure.
Check if the interface group/zone called "outside" contains both port1 and port2 - I would suspect that is not the case, based on the logs.
Best regards,
Markus
Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.