Custom Parser Error
 Hello Team,
Hello Team,
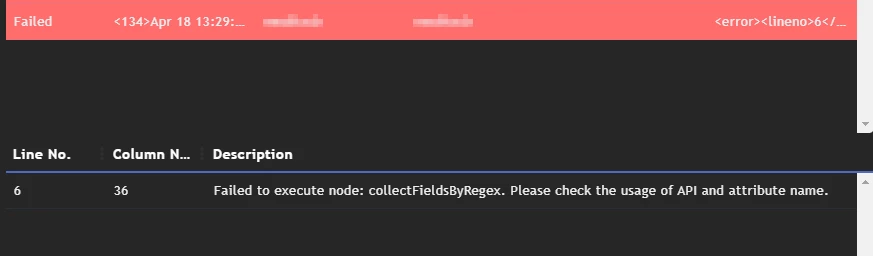
I am new to FortiSIEM and i could be making some obvious mistake but kindly help. We onboarded a custom application onto FSM and wanted to build custom parser so that we can get notified of failed logins. I tried building one and i Keep running into the same issue "Failed to execute node: collectFieldsByRegex. Please check the usage of API and attribute name." Not sure why.. My xml is as below:
<eventFormatRecognizer><![CDATA[SOE: BAD\s+]]></eventFormatRecognizer> <parsingInstructions> <collectFieldsByRegex src="$_rawmsg"> <regex><![CDATA[<:gPatSyslogPRI><_mon:gPatMon>\s+<_day:gPatDay>\s+<_time:gPatTime>\s+<reptDevName:gPatHostName>\s+SOE:\s+<_body:gPatMesgBody>]]></regex> </collectFieldsByRegex> <collectFieldsByRegex src="$_body"> <regex><![CDATA[?:SIGN-ON <srcIpAddr:gPatIpAddr>\s+\(<:gPatStr>\)\s+<:gPatStr>\s+-\s+d+\s+<:gPatStr>\.<:gPatStr>:\s+<:gPatStr>\s+<:gPatStr>]]></regex> </collectFieldsByRegex> <setEventAttribute attr="eventType">Custom App: Failed Login</setEventAttribute> <setEventAttribute attr="eventSeverity">1</setEventAttribute> </parsingInstructions>
The Logs am trying to Parse are as below. Changed a few things due to privacy reasons
<134>Apr 20 19:53:14 computerA SOE: BAD SIGN-ON 0T2.2.2.2.1 (CAP34.2.1) CAP34.2 - 1 APP1.MIS: APP1 USERNAME1 <134>Apr 20 19:05:22 computerA SOE: BAD SIGN-ON 9N0T2.3.3.3.1 (THOR1.3.1) THOR1.3 - 1 MICRO PC APP2.MIS: APP2 USERNAME3 USERNAME3 USERNAME3 <134>Apr 19 19:24:29 computerC SOE: BAD SIGN-ON 9N0T1.1.14.1.1 (SPI2.1.1) SPI2.1 - 1 APP3.MIS: APP3 USERNAME44 USERNAME44 USERNAME44 <134>Apr 19 16:42:45 computerD SOE: BAD SIGN-ON 7N0T4.1.4.1.2 (IRN22.1.2) IRN22.1 - 2 APP3.MIS: APP3 USERNAME55 USERNAME55 USERNAME55

