- Support Forum
- Knowledge Base
- Customer Service
- Internal Article Nominations
- FortiGate
- FortiClient
- FortiADC
- FortiAIOps
- FortiAnalyzer
- FortiAP
- FortiAuthenticator
- FortiBridge
- FortiCache
- FortiCare Services
- FortiCarrier
- FortiCASB
- FortiConverter
- FortiCNP
- FortiDAST
- FortiData
- FortiDDoS
- FortiDB
- FortiDNS
- FortiDLP
- FortiDeceptor
- FortiDevice
- FortiDevSec
- FortiDirector
- FortiEdgeCloud
- FortiEDR
- FortiEndpoint
- FortiExtender
- FortiGate Cloud
- FortiGuard
- FortiGuest
- FortiHypervisor
- FortiInsight
- FortiIsolator
- FortiMail
- FortiManager
- FortiMonitor
- FortiNAC
- FortiNAC-F
- FortiNDR (on-premise)
- FortiNDRCloud
- FortiPAM
- FortiPhish
- FortiPortal
- FortiPresence
- FortiProxy
- FortiRecon
- FortiRecorder
- FortiSRA
- FortiSandbox
- FortiSASE
- FortiSASE Sovereign
- FortiScan
- FortiSIEM
- FortiSOAR
- FortiSwitch
- FortiTester
- FortiToken
- FortiVoice
- FortiWAN
- FortiWeb
- FortiAppSec Cloud
- Lacework
- Wireless Controller
- RMA Information and Announcements
- FortiCloud Products
- ZTNA
- 4D Documents
- Customer Service
- Community Groups
- Blogs
- Fortinet Community
- Support Forum
- FortiManager - VPN Manager Tunnel ID
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
FortiManager - VPN Manager Tunnel ID
Hi ,
We are setting up a Hub and Spoke architecture, and Spoke to Spoke through the ADVPN (we have almost 100 remote sites), with 3 links for the SD WAN.
We used the FortiManager, and we created 3 community in dial up for the three links, on the other hand we just have a difficulty to put a name to the tunnel which is created with a random ID, suddenly we cannot associate them with SD-WAN interfaces.
How can we proceed please.
Thank you community.
- Labels:
-
FortiGate
-
FortiManager
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @ys1
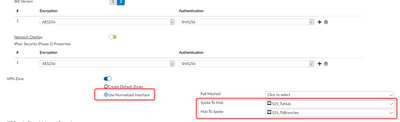
Use normalized Interfaces in the VPN configuration.
You find this option in "VPN Manager->Edit VPN Community"
Afterwards you can use this normalized interface in the SD-WAN configuration.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @scan888 ;
Thank you for your response,
we have already try this, but, when we use normalized "VPNZone" he create a zone interface, and note an SD WAN , our need is when the tunnel is created, he automatically associated to the SD WAN zone, and not an interface Zone.
Thank you for your support,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
you are encountering an issue with naming VPN tunnels in FortiManager when using ADVPN for Hub and Spoke architecture with SD-WAN. Specifically, you are having difficulty assigning a name to the VPN tunnel created with a random ID.
Here are some steps you can take to resolve this issue:
1. Verify that the VPN configuration on the FortiManager and FortiGate devices is correct. Make sure that the community settings, SD-WAN interface settings, and VPN settings are all configured correctly.
2. Check that the tunnel ID is unique and not shared with any other VPN tunnels. If there are multiple VPN tunnels with the same ID, it can cause issues with naming and associating the tunnels with SD-WAN interfaces.
3. Consider using a naming convention for the VPN tunnels that includes the community name, SD-WAN interface, and tunnel ID. This can help ensure that the VPN tunnels are named consistently and can be associated with the correct SD-WAN interfaces.
4. If you are still having difficulty assigning a name to the VPN tunnel, consider reaching out to Fortinet support for further assistance. They may be able to provide more specific guidance based on your specific situation.
By following these steps, you can resolve the issue with naming VPN tunnels in FortiManager when using ADVPN for Hub and Spoke architecture with SD-WAN.
Faizal Emam
-
FortiGate
11,214 -
FortiClient
2,309 -
FortiManager
939 -
FortiAnalyzer
709 -
5.2
687 -
5.4
638 -
FortiClient EMS
621 -
FortiSwitch
619 -
FortiAP
586 -
IPsec
491 -
SSL-VPN
422 -
6.0
416 -
FortiMail
393 -
5.6
362 -
FortiNAC
327 -
FortiWeb
274 -
6.2
251 -
FortiAuthenticator v5.5
234 -
SD-WAN
220 -
FortiAuthenticator
200 -
FortiGuard
169 -
FortiGate-VM
168 -
Firewall policy
155 -
5.0
152 -
6.4
128 -
FortiCloud Products
122 -
FortiSIEM
121 -
FortiToken
118 -
FortiGateCloud
113 -
High Availability
100 -
Wireless Controller
99 -
Customer Service
91 -
SAML
88 -
Routing
85 -
ZTNA
85 -
FortiProxy
81 -
Authentication
81 -
FortiADC
78 -
BGP
76 -
VLAN
76 -
Certificate
76 -
DNS
75 -
Fortivoice
74 -
FortiEDR
74 -
LDAP
71 -
RADIUS
69 -
FortiLink
65 -
SSO
63 -
NAT
59 -
FortiSandbox
58 -
Interface
57 -
Application control
55 -
FortiExtender
54 -
VDOM
53 -
4.0MR3
49 -
Virtual IP
49 -
Logging
45 -
FortiDNS
43 -
FortiPAM
42 -
SSL SSH inspection
42 -
Web profile
39 -
FortiGate v5.4
38 -
FortiSwitch v6.4
38 -
Automation
37 -
FortiConnect
36 -
FortiConverter
33 -
FortiWAN
32 -
API
32 -
Traffic shaping
29 -
FortiGate v5.2
28 -
FortiGate Cloud
28 -
Static route
28 -
SSID
27 -
SNMP
26 -
System settings
25 -
OSPF
24 -
FortiSwitch v6.2
23 -
FortiPortal
23 -
WAN optimization
23 -
Web application firewall profile
23 -
FortiMonitor
21 -
Security profile
21 -
IP address management - IPAM
21 -
Web rating
20 -
FortiSOAR
19 -
FortiAP profile
18 -
Explicit proxy
17 -
Admin
17 -
Intrusion prevention
17 -
FortiGate v5.0
16 -
FortiDDoS
16 -
IPS signature
16 -
FortiManager v4.0
15 -
NAC policy
15 -
Users
15 -
Traffic shaping policy
15 -
Proxy policy
15 -
FortiManager v5.0
14 -
FortiCASB
14 -
DNS filter
13 -
FortiDeceptor
12 -
Fabric connector
12 -
Port policy
12 -
FortiWeb v5.0
11 -
FortiBridge
11 -
trunk
11 -
Traffic shaping profile
11 -
Authentication rule and scheme
11 -
FortiAnalyzer v5.0
10 -
FortiRecorder
10 -
Fortinet Engage Partner Program
10 -
FortiGate v4.0 MR3
9 -
RMA Information and Announcements
9 -
Antivirus profile
9 -
Application signature
9 -
FortiCache
8 -
FortiToken Cloud
8 -
Packet capture
8 -
Vulnerability Management
8 -
4.0
7 -
4.0MR2
7 -
FortiNDR
7 -
VoIP profile
7 -
FortiScan
6 -
FortiTester
6 -
DoS policy
6 -
FortiCarrier
5 -
DLP profile
5 -
DLP sensor
5 -
Email filter profile
5 -
Protocol option
5 -
TACACS
5 -
Service
5 -
Cloud Management Security
5 -
3.6
4 -
FortiHypervisor
4 -
FortiDirector
4 -
Internet service database
4 -
DLP Dictionary
4 -
Netflow
4 -
Replacement messages
4 -
SDN connector
4 -
Multicast routing
4 -
FortiDB
3 -
FortiAI
3 -
Kerberos
3 -
Video Filter
3 -
File filter
3 -
Multicast policy
3 -
Zone
3 -
FortiEdge Cloud
3 -
FortiInsight
2 -
Schedule
2 -
ICAP profile
2 -
Virtual wire pair
2 -
Lacework
2 -
FortiGuest
2 -
FortiEdge
2 -
4.0MR1
1 -
FortiManager-VM
1 -
FortiCWP
1 -
Subscription Renewal Policy
1 -
FortiSASE
1 -
FortiPresence
1 -
FortiAIOps
1
| User | Count |
|---|---|
| 2931 | |
| 1460 | |
| 869 | |
| 826 | |
| 455 |
The Fortinet Security Fabric brings together the concepts of convergence and consolidation to provide comprehensive cybersecurity protection for all users, devices, and applications and across all network edges.
Copyright 2026 Fortinet, Inc. All Rights Reserved.