- Support Forum
- Knowledge Base
- Customer Service
- Internal Article Nominations
- FortiGate
- FortiClient
- FortiADC
- FortiAIOps
- FortiAnalyzer
- FortiAP
- FortiAuthenticator
- FortiBridge
- FortiCache
- FortiCare Services
- FortiCarrier
- FortiCASB
- FortiConverter
- FortiCNP
- FortiDAST
- FortiData
- FortiDDoS
- FortiDB
- FortiDNS
- FortiDLP
- FortiDeceptor
- FortiDevice
- FortiDevSec
- FortiDirector
- FortiEdgeCloud
- FortiEDR
- FortiEndpoint
- FortiExtender
- FortiGate Cloud
- FortiGuard
- FortiGuest
- FortiHypervisor
- FortiInsight
- FortiIsolator
- FortiMail
- FortiManager
- FortiMonitor
- FortiNAC
- FortiNAC-F
- FortiNDR (on-premise)
- FortiNDRCloud
- FortiPAM
- FortiPhish
- FortiPortal
- FortiPresence
- FortiProxy
- FortiRecon
- FortiRecorder
- FortiSRA
- FortiSandbox
- FortiSASE
- FortiSASE Sovereign
- FortiScan
- FortiSIEM
- FortiSOAR
- FortiSwitch
- FortiTester
- FortiToken
- FortiVoice
- FortiWAN
- FortiWeb
- FortiAppSec Cloud
- Lacework
- Wireless Controller
- RMA Information and Announcements
- FortiCloud Products
- ZTNA
- 4D Documents
- Customer Service
- Community Groups
- Agora
- Engage Services
- The EPSP Platform
- The ETSP Platform
- Finland
- FortiCare Service Development
- FortiGate-VM on Azure
- FortiGate-VM on AWS
- FortiGate CNF (All Marketplaces)
- FortiWeb Cloud (All Marketplaces)
- Fortinet for SAP
- FortiSIEM
- FortiSOAR
- KCS
- Lacework
- Super User
- Agora
- Engage Services
- The EPSP Platform
- The ETSP Platform
- Finland
- FortiCare Service Development
- FortiGate-VM on Azure
- FortiGate-VM on AWS
- FortiGate CNF (All Marketplaces)
- FortiWeb Cloud (All Marketplaces)
- Fortinet for SAP
- FortiSIEM
- FortiSOAR
- KCS
- Lacework
- Super User
- Agora
- Blogs
- Fortinet Community
- Support Forum
- Forticlient VPN - SAML SSO Azure AD - credentials ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Forticlient VPN - SAML SSO Azure AD - credentials cache
Hi to everybody,
one of my customer has this problem:
We have implemented SAML SSO login in a Fortigate unit (Fortigate VM00) where Azure AD acts as SAML IdP
Everything works fine except we have a "strange" behavior with Forticlient VPN.
Seems Fortigate VPN makes a sort of credential cache.
After a user makes logout, if he tries to reconnect, the authentication phase is skipped.
This happens only if Forticlient VPN interface is not close.
If the user, after a disconnect / logout, closes the Forticlient VPN interface , when he tries to reconnect he must follow the authentication steps.
Seems this cache is done by the lock file inside C:\users\(username)\appData\Local\FortiClient
Everytime Forticlient VPN interface is closed, this file is deleted.
Seems that, until the lock file exists, the session between forticlient and microsoft is kept open (if he clicks disconnect, the session is close between laptop and fortigate firewall but not beween laptop and microsoft)
In order to close this "persistent session", is enough to close the login form
I have opened a TT with Fortinet support but Forticlient VPN is not a "paid product" and they can't help me directly. They suggested me to open here my case.....
Somebody else has the same issue?
Regards
Marco
- Labels:
-
FortiClient
-
FortiGate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also noticed this and would be interested in a solution
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey Marco,
as far as I know: If FortiClient is not closed properly, it will still have the SAML cookie stored (and Azure SAML IdP will also still have the SAML session, as no logout was sent to it).
When establishing VPN again, FortiGate will redirect the client to Azure for SAML login, and at that point FortiClient will present the stored cookie, which Azure will accept because it also still has the SAML session, and the user is considered logged in without needing to input credentials.
-> if you clear the existing session in Azure, that should also enforce a new login
-> I tested this a bit with FortiAuthenticator serving as IdP; FortiAuthenticator retained an IdP session for the FortiClient login unless there was a proper logout with a SAML assertion sent to the IdP logout URL; I assume Azure behaves similarly with retaining the session until it times out if no explicit assertion was sent to the logout URL.
I'm not aware of any configuration option to have FortiClient purge its cache if SSLVPN is dropped instead of properly logged out, and there is no setting on FortiGate to have it send a logout request to Azure SAML IdP if VPN drops.
This would probably require some kind of feature request to straighten out.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Debbie_FTNT ,
what do you mean with "FortiClient is not closed properly" ?
The VPN is closes properly. The customer clicks disconnect on Forticlient VPN interface.
The only problem is, if he doesn't close this interface, in case he does reconnect, the authentication is skypped. In case he closes Forticlient VPN interface / form (not close application on system tray.. the application is still open on background) and reopen it, the authentication is required again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can set up a disconnect script "del /s C:\users\%username%\AppData\Local\FortiClient\cookies". This works for Windows, have not found the solution for a mac. It appears that it runs even if the VPN drops, due to a connectivity issue.
Created on 05-15-2022 08:48 PM Edited on 05-15-2022 08:48 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, do you have any idea where those cookies are stored on Ubuntu?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Deleting the Cookies and Cookies-Journal files for sure forces re-authentication.
Q.
Do you know how long the cookie persists. Kept the cookies for over a week or two and I still do not need to reauthenticate?
Q.
As a half way house, is there anyway the UPN is preserved always so users only need to enter their password and MFA?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here is how i was able to resolve this through Group Policy.
First created a simple .bat file that does 2 things:
-Kills forticlient.exe
-Deletes Cookies and Cookies-journal files
Save the following as forticlient_delete_cookies.bat
-----------------------------
This closes the Forticlient Console GUI as it is using the required files we need to delete. The user will stay connected to vpn and this will not interfere with their established connection, and just need to relaunch shortcut or open from app tray in bottom right corner of screen to bring the gui back up.
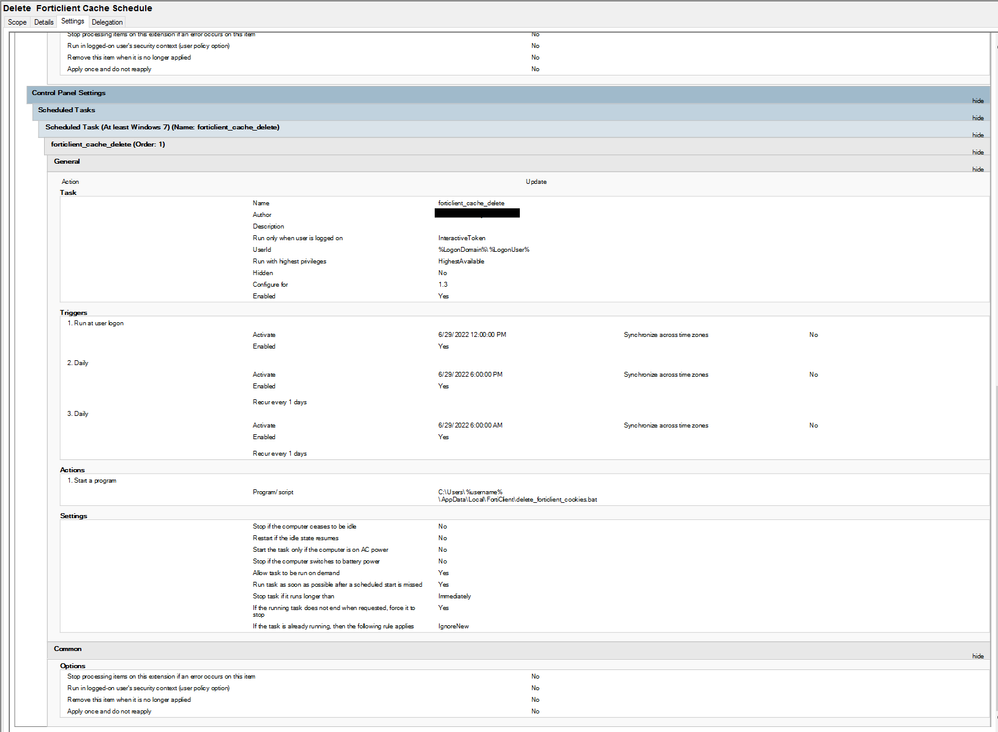
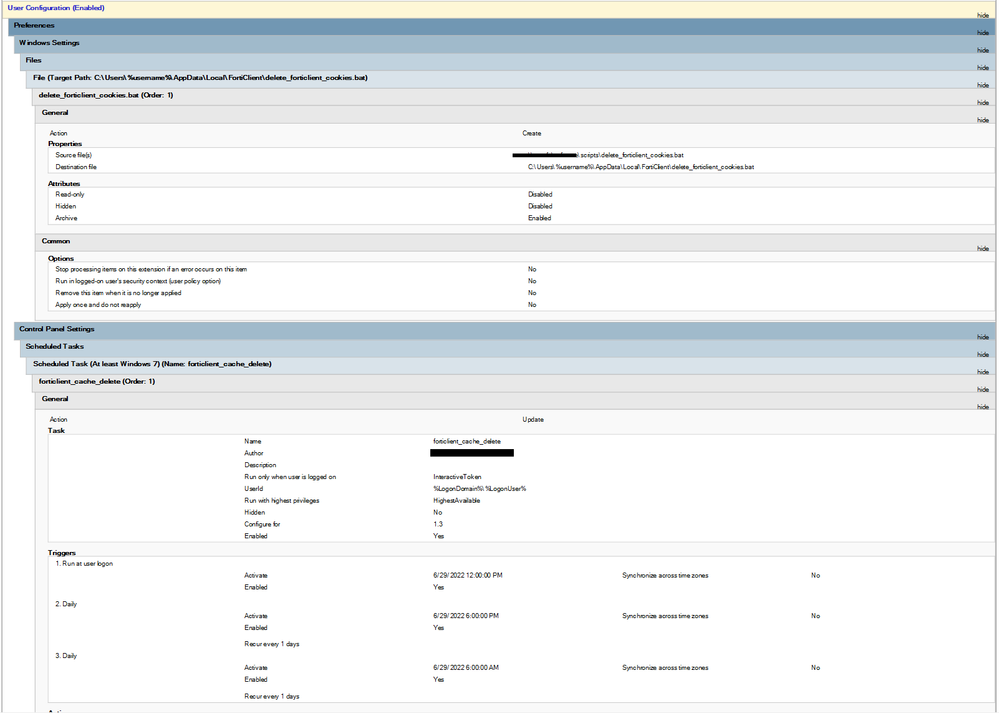
Tested in a new GPO over VPN with a user that has no administrator permissions to machine.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Brilliant!
Thanks for the detailed breakdown which I will take a look at.
For me, I am keen to preserve the UPN element when users next sign on so all they need to is
enter in their password (or matching code number).
Right now I have DUO set up for MFA with the password cached so all users do is authorise the push authentication prompt on their DUO mobile app.
Just trying to balance convenience with security. Suspect users will baulk at the idea of enter of all the extra steps they would need to do to sign in via Azure SSO.
Preserving the UPN is the halfway house I am after.
As I understand it, you do need FortiOS 7.x as well (to read and presence the user agent string) but I am only running 6.x on the Firewall at the moment.
Since users login using Windows hello PIN code, I am aiming for passwordless authentication for the VPN as well, hence the move to SAML authentication.
-
FortiGate
11,179 -
FortiClient
2,301 -
FortiManager
937 -
FortiAnalyzer
709 -
5.2
687 -
5.4
638 -
FortiClient EMS
619 -
FortiSwitch
617 -
FortiAP
585 -
IPsec
489 -
SSL-VPN
418 -
6.0
416 -
FortiMail
391 -
5.6
362 -
FortiNAC
326 -
FortiWeb
274 -
6.2
251 -
FortiAuthenticator v5.5
234 -
SD-WAN
219 -
FortiAuthenticator
199 -
FortiGate-VM
168 -
FortiGuard
168 -
Firewall policy
155 -
5.0
152 -
6.4
128 -
FortiCloud Products
122 -
FortiSIEM
121 -
FortiToken
118 -
FortiGateCloud
113 -
Wireless Controller
99 -
High Availability
99 -
Customer Service
91 -
SAML
87 -
Routing
85 -
ZTNA
85 -
FortiProxy
81 -
Authentication
81 -
FortiADC
77 -
BGP
76 -
VLAN
76 -
DNS
75 -
Certificate
75 -
Fortivoice
73 -
FortiEDR
73 -
LDAP
70 -
RADIUS
69 -
FortiLink
64 -
SSO
63 -
NAT
59 -
FortiSandbox
58 -
Interface
57 -
Application control
55 -
FortiExtender
53 -
VDOM
52 -
4.0MR3
49 -
Virtual IP
49 -
Logging
45 -
FortiDNS
43 -
FortiPAM
42 -
SSL SSH inspection
42 -
Web profile
39 -
FortiGate v5.4
38 -
FortiSwitch v6.4
38 -
Automation
37 -
FortiConnect
36 -
FortiConverter
33 -
FortiWAN
32 -
API
32 -
Traffic shaping
29 -
FortiGate v5.2
28 -
FortiGate Cloud
28 -
Static route
28 -
SSID
27 -
SNMP
26 -
System settings
25 -
OSPF
24 -
FortiSwitch v6.2
23 -
FortiPortal
23 -
WAN optimization
23 -
Web application firewall profile
23 -
FortiMonitor
21 -
IP address management - IPAM
21 -
Security profile
20 -
Web rating
20 -
FortiSOAR
19 -
FortiAP profile
18 -
Admin
17 -
Intrusion prevention
17 -
FortiGate v5.0
16 -
FortiDDoS
16 -
Explicit proxy
16 -
IPS signature
16 -
FortiManager v4.0
15 -
NAC policy
15 -
Users
15 -
Traffic shaping policy
15 -
Proxy policy
15 -
FortiManager v5.0
14 -
FortiCASB
14 -
DNS filter
13 -
FortiDeceptor
12 -
Fabric connector
12 -
Port policy
12 -
FortiWeb v5.0
11 -
FortiBridge
11 -
trunk
11 -
Traffic shaping profile
11 -
Authentication rule and scheme
11 -
FortiAnalyzer v5.0
10 -
FortiRecorder
10 -
Fortinet Engage Partner Program
10 -
FortiGate v4.0 MR3
9 -
RMA Information and Announcements
9 -
Antivirus profile
9 -
Application signature
9 -
FortiCache
8 -
FortiToken Cloud
8 -
Packet capture
8 -
Vulnerability Management
8 -
4.0
7 -
4.0MR2
7 -
FortiNDR
7 -
VoIP profile
7 -
FortiScan
6 -
FortiTester
6 -
DoS policy
6 -
FortiCarrier
5 -
DLP profile
5 -
DLP sensor
5 -
Email filter profile
5 -
Protocol option
5 -
TACACS
5 -
Service
5 -
Cloud Management Security
5 -
3.6
4 -
FortiHypervisor
4 -
FortiDirector
4 -
Internet service database
4 -
DLP Dictionary
4 -
Netflow
4 -
Replacement messages
4 -
SDN connector
4 -
Multicast routing
4 -
FortiDB
3 -
FortiAI
3 -
Kerberos
3 -
Video Filter
3 -
File filter
3 -
Multicast policy
3 -
Zone
3 -
FortiEdge Cloud
3 -
FortiInsight
2 -
Schedule
2 -
ICAP profile
2 -
Virtual wire pair
2 -
Lacework
2 -
FortiGuest
2 -
FortiEdge
2 -
4.0MR1
1 -
FortiManager-VM
1 -
FortiCWP
1 -
Subscription Renewal Policy
1 -
FortiSASE
1 -
FortiPresence
1 -
FortiAIOps
1
| User | Count |
|---|---|
| 2919 | |
| 1452 | |
| 855 | |
| 826 | |
| 455 |
The Fortinet Security Fabric brings together the concepts of convergence and consolidation to provide comprehensive cybersecurity protection for all users, devices, and applications and across all network edges.
Copyright 2026 Fortinet, Inc. All Rights Reserved.