Technical Note : Configuring Authentication Based Routing
Description
Scope
Solution
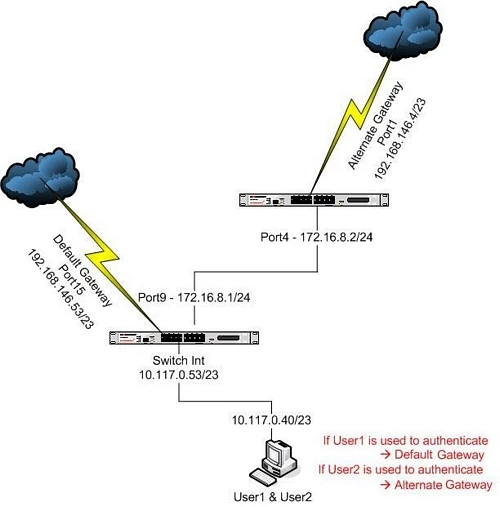
Authentication-Based Routing allows the creation of an identity-based route that associates a user group with one or more routes. This is currently only configurable via the CLI.
It is useful for MSSPs that need to route users from different organization to different Internet gateways and it works with Local or Remote Authentication.
It should be noted that this feature is only available when Identity-based Policy is enabled.
Scope
FortiGate v5.0 and above
Solution
Configuration Example
1. Create a local user(s). Local user configuration:
config user local
edit "user1"
set type password
set passwd <password>
next
edit "user2"
set type password
set passwd <password>
end
end
2. Create a user group. User group configuration:
config user group
edit "test1"
set member "user1"
next
edit "test2"
set member "user2"
end
end
3. Configure an Identity-based Routing entry. A sample configuration for creating an Identity Based Route is given below:
config firewall identity-based-route
edit "alternate-route"
config rule
edit 1
set gateway 172.16.8.2
set device "port9"
set groups "test1" "test2"
next
end
end
end
4. Enable Identity Based Routing on the corresponding firewall policy. Note the setting of 'set idnetity-based-route'.
config firewall policy
edit 4
set srcintf "switch"
set dstintf "port15"
set srcaddr "all"
set action accept
set device-visibility enable
set user-visibility enable
set identity-based-route "alternate-route"
set identity-based enable
set nat enable
config identity-based-policy
edit 1
set schedule "always"
set logtraffic enable
set groups "test1"
set dstaddr "all"
set service "ANY"
next
edit 2
set schedule "always"
set logtraffic enable
set groups "test2"
set dstaddr "all"
set service "ANY"
end
end
end
end
5. Create another firewall policy to allow traffic to flow out to the alternate gateway:
edit 2
set srcintf "switch"
set dstintf "port9"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set service "ANY"
set device-visibility enable
set user-visibility enable
set nat enable
end
Verification:
1. Log in with the corresponding user
2. Run a Debug Flow to verify that the traffic is going on on the correct gateway with the user
3. Run a PING or generate some traffic to the internet. Below are some sample output:
- Traffic going out the default gateway:
id=36871 trace_id=90 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=90 msg="allocate a new session-000019f9"
id=36871 trace_id=90 msg="find a route: gw-192.168.147.254 via port15"
id=36871 trace_id=90 msg="find SNAT: IP-192.168.146.53, port-62464"
id=36871 trace_id=90 msg="Allowed by Policy-4: SNAT"
id=36871 trace_id=90 msg="SNAT 10.117.0.40->192.168.146.53:62464"
id=36871 trace_id=91 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->192.168.146.53:0) from port15."
id=36871 trace_id=91 msg="Find an existing session, id-000019f9, reply direction"
id=36871 trace_id=91 msg="DNAT 192.168.146.53:0->10.117.0.40:768"
id=36871 trace_id=91 msg="find a route: gw-10.117.0.40 via switch"
id=36871 trace_id=92 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=92 msg="Find an existing session, id-000019f9, original direction"
id=36871 trace_id=92 msg="SNAT 10.117.0.40->192.168.146.53:62464"
id=36871 trace_id=93 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->192.168.146.53:0) from port15."
id=36871 trace_id=93 msg="Find an existing session, id-000019f9, reply direction"
id=36871 trace_id=93 msg="DNAT 192.168.146.53:0->10.117.0.40:768"
id=36871 trace_id=94 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=94 msg="Find an existing session, id-000019f9, original direction"
id=36871 trace_id=94 msg="SNAT 10.117.0.40->192.168.146.53:62464"
id=36871 trace_id=95 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->192.168.146.53:0) from port15."
id=36871 trace_id=95 msg="Find an existing session, id-000019f9, reply direction"
id=36871 trace_id=95 msg="DNAT 192.168.146.53:0->10.117.0.40:768"
id=36871 trace_id=96 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=96 msg="Find an existing session, id-000019f9, original direction"
id=36871 trace_id=96 msg="SNAT 10.117.0.40->192.168.146.53:62464"
id=36871 trace_id=97 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->192.168.146.53:0) from port15."
id=36871 trace_id=97 msg="Find an existing session, id-000019f9, reply direction"
id=36871 trace_id=97 msg="DNAT 192.168.146.53:0->10.117.0.40:768"
- Traffic going out the alternate gateway:
id=36871 trace_id=98 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=98 msg="allocate a new session-00001a42"
id=36871 trace_id=98 msg="find a route: gw-172.16.8.2 via port9"
id=36871 trace_id=98 msg="find SNAT: IP-172.16.8.1, port-62464"
id=36871 trace_id=98 msg="Allowed by Policy-2: SNAT"
id=36871 trace_id=98 msg="SNAT 10.117.0.40->172.16.8.1:62464"
id=36871 trace_id=99 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->172.16.8.1:0) from port9."
id=36871 trace_id=99 msg="Find an existing session, id-00001a42, reply direction"
id=36871 trace_id=99 msg="DNAT 172.16.8.1:0->10.117.0.40:768"
id=36871 trace_id=99 msg="find a route: gw-10.117.0.40 via switch"
id=36871 trace_id=100 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=100 msg="Find an existing session, id-00001a42, original direction"
id=36871 trace_id=100 msg="enter fast path"
id=36871 trace_id=100 msg="SNAT 10.117.0.40->172.16.8.1:62464"
id=36871 trace_id=101 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->172.16.8.1:0) from port9."
id=36871 trace_id=101 msg="Find an existing session, id-00001a42, reply direction"
id=36871 trace_id=101 msg="enter fast path"
id=36871 trace_id=101 msg="DNAT 172.16.8.1:0->10.117.0.40:768"
id=36871 trace_id=102 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=102 msg="Find an existing session, id-00001a42, original direction"
id=36871 trace_id=102 msg="enter fast path"
id=36871 trace_id=102 msg="SNAT 10.117.0.40->172.16.8.1:62464"
id=36871 trace_id=103 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->172.16.8.1:0) from port9."
id=36871 trace_id=103 msg="Find an existing session, id-00001a42, reply direction"
id=36871 trace_id=103 msg="enter fast path"
id=36871 trace_id=103 msg="DNAT 172.16.8.1:0->10.117.0.40:768"
id=36871 trace_id=104 msg="vd-root received a packet(proto=1, 10.117.0.40:768->8.8.8.8:8) from switch."
id=36871 trace_id=104 msg="Find an existing session, id-00001a42, original direction"
id=36871 trace_id=104 msg="enter fast path"
id=36871 trace_id=104 msg="SNAT 10.117.0.40->172.16.8.1:62464"
id=36871 trace_id=105 msg="vd-root received a packet(proto=1, 8.8.8.8:62464->172.16.8.1:0) from port9."
id=36871 trace_id=105 msg="Find an existing session, id-00001a42, reply direction"
id=36871 trace_id=105 msg="enter fast path"
id=36871 trace_id=105 msg="DNAT 172.16.8.1:0->10.117.0.40:768"
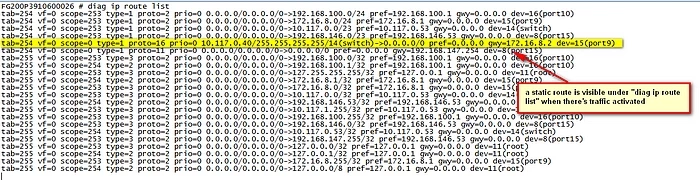
4. Run a "diag ip route list", if configured correctly and when there is active traffic hitting the authentication-based routing, an entry as shown below should be seen: