SSL for HTTPS
Hi all,
I'm having some issues with port forwarding. I'm running fortinet v7.0.5. I have a Windows Server running Tomcat 8.5 which is running my website. I've succesfully managed to import my SSL certificates into tomcat (on my windows server, going into https://localhost:8443/ i can see the certificate (shows as error, because the domain doesnt match, but all of the information about the CA etc is there, so its working okay). But when i go through https://domain.com:8443/ i get Unable to connect - An error occurred during a connection to domain.com. If i go to https://domain.com (without the port) i get The connection has timed out - An error occurred during a connection to
Now i have a public ip on my fortinet wan, which is used mostly just for ssl-vpn to remote into my workspace when im at home.
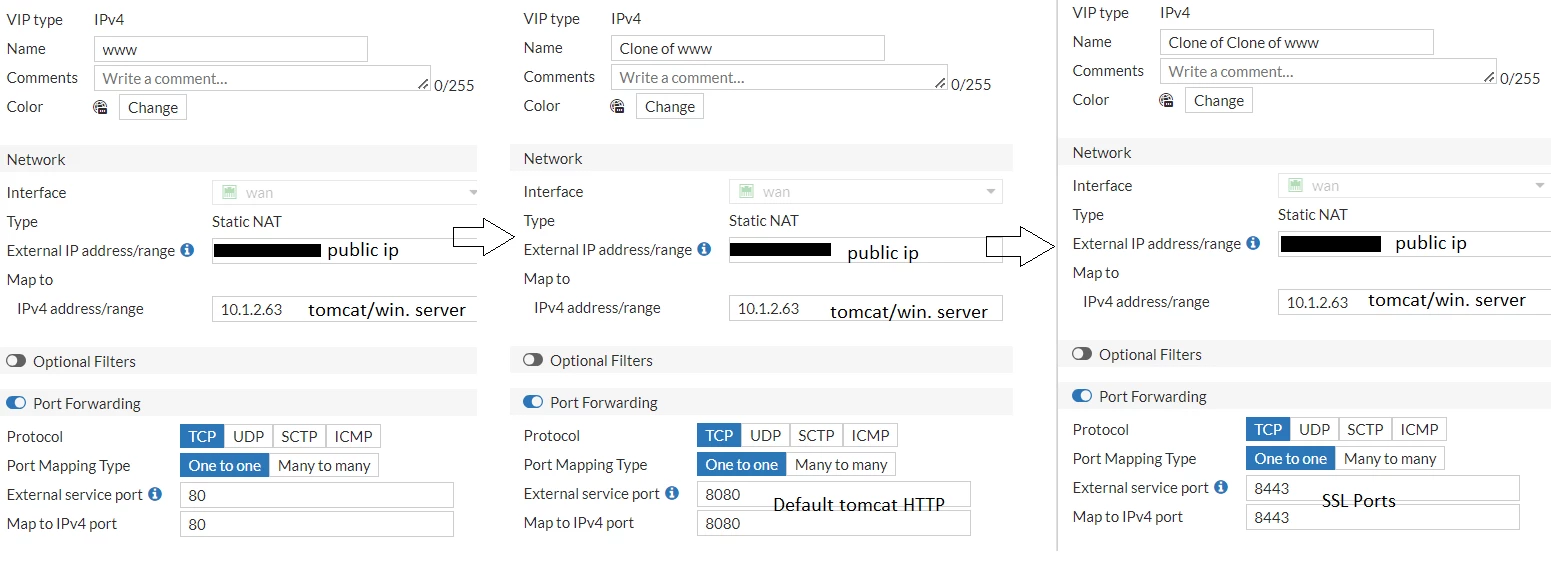
I've added 2 VIP's one for port 80 and one for port 8443(https) - port 8443 seems to get hits, but cant load, and port 8443 reports as closed when using tools to check for open ports.
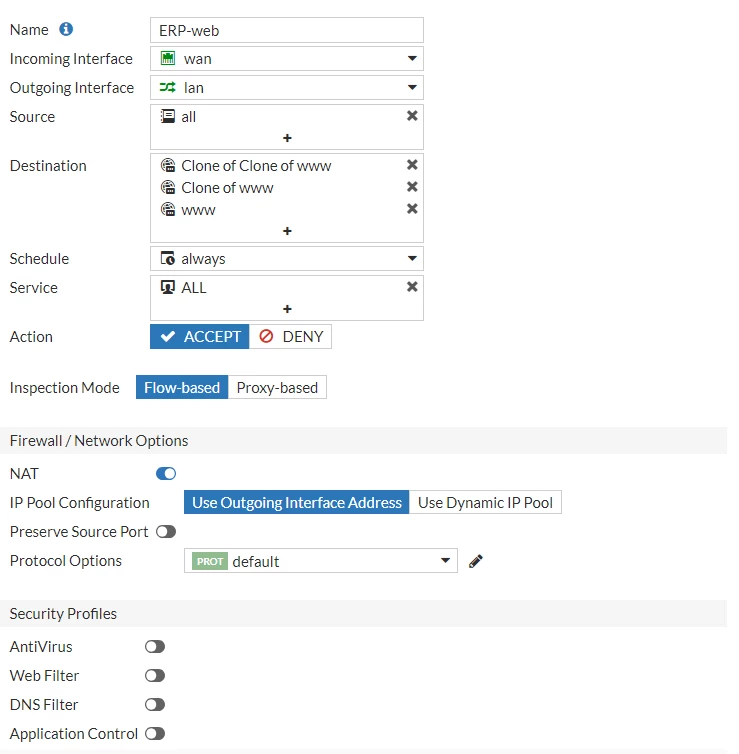
I've attached some screenshots of my vip's and firewall policies (im guessing the issue might be within the firewall rules, as im a complete newbie at this).
I've attached 2 screenshots - 1 of the vip settings, and other of the firewall rule. I would greatly appreciate if someone more experienced could point be to the right direction, i've fought this for 3 days without any luck.
If you require any more information, please do say and i will provide them!
Many thanks!
screenshots: