- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
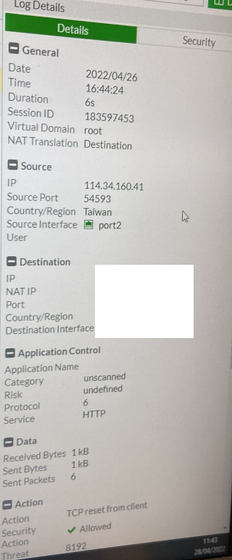
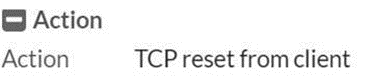
IPS engine blocked the attack but "Allowed" & Action "TCP reset from client" in Traffic log
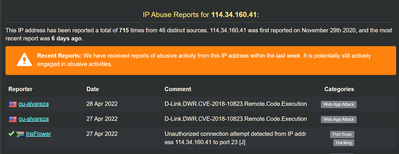
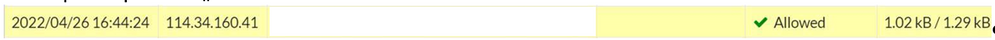
Recently the FortiGate received attack from 114.34.160.41 and IPS successfully blocked the attack, but then caused a false alarm on SIEM.
As the FortiGate sent a “Allowed – session reset” log message to SIEM, the SIEM triggered a high-alert message, which the keyword “allowed” made a confuse of the Firewall bypassed the attack.
Any suggestion to prevent that? Thanks.
Solved! Go to Solution.
- Labels:
-
FortiGate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
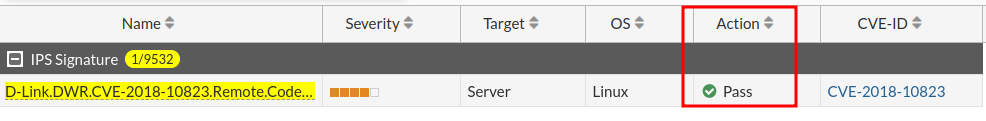
Are you sure the IPS blocked this?
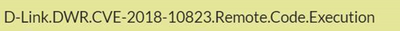
The default action for this signature is to allow:
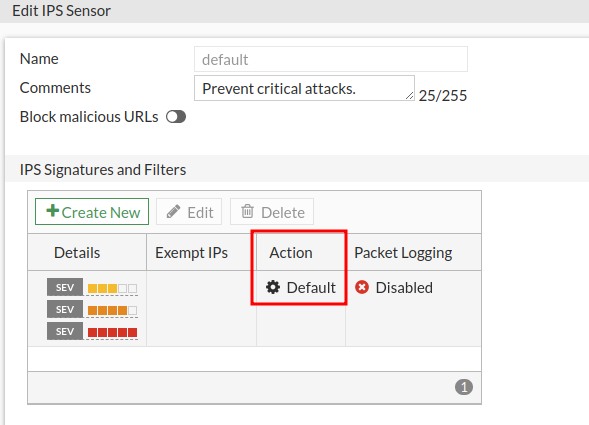
From the IPS log it looks like you're using the default IPS profile, which has the action set to default (which means do whatever the individual signature's default action is, which in this case is allow):
Could you confirm what the action was in the IPS log you had above? Your picture didn't show the full log.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you sure the IPS blocked this?
The default action for this signature is to allow:
From the IPS log it looks like you're using the default IPS profile, which has the action set to default (which means do whatever the individual signature's default action is, which in this case is allow):
Could you confirm what the action was in the IPS log you had above? Your picture didn't show the full log.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi amouawad,
Thanks for your reply! The policy is using default IPS profile and should be the reason why action shows "Allowed" on traffic log.
But why some CVE set Action "Pass" as default setting?